Home / [Edit] For Employer
EVIDENCE-BASED HIRING
Hire-Ready Cybersecurity Professionals.
Not Resumes. Real Experience.
We ensure our candidates are “hire-ready” with professional resumes,
portfolios, interview training, and hands-on experience using various platforms
in our organizations production environment.
No commitment required — just tell us your stack and hiring needs.
THE CHALLENGE WE'RE ALL FACING
Hiring in cybersecurity feels broken.
I’ve talked to hundreds of hiring managers, and they all tell me the same story. Candidates interview well, the resume checks all the boxes, but when they start, there’s a gap. Sometimes a big one. Meanwhile, talented career-changers who could do the job get filtered out because they don’t have the “right” keywords or years of experience. It’s frustrating for everyone.
1
The Resume Problem
Everyone lists the same tools and certifications. How do you know who can actually configure a SIEM or analyze logs without spending weeks training them?
2
Time & Resources
Your team doesn’t have bandwidth to onboard someone who needs months of hand-holding. You need people who can contribute from week one, not month six.
3
Hidden Potential
Some of the best security professionals I know came from non-traditional backgrounds. But they get filtered out by automated systems before anyone sees what they can do.
and interviews that
can't verify real skills.
evidence over claims.
Every candidate proves their skills
in a live production environment.
VERIFIED CAPABILITIES
What "Evidence-Based" Actually Means
Every candidate delivers a digital portfolio proving hands-on execution in production-grade environments. No embellishment. No keyword stuffing.
GITHUB VERIFIED
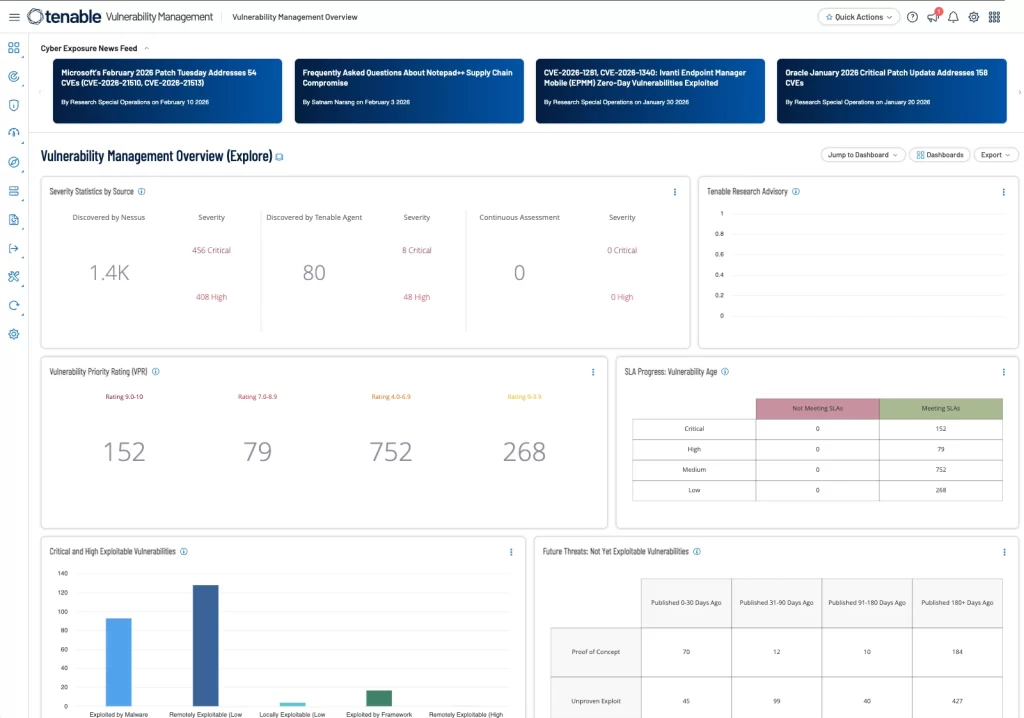
Vulnerability Scanning and Remediation with Tenable
Students train on an enterprise-licensed Tenable instance to perform vulnerability scanning and programmatic remediation across both Windows and Linux environments. All BASH and PowerShell remediation scripts are documented and maintained in GitHub. Training goes beyond the technical — every student also develops the soft skills of vulnerability management, including risk communication, prioritization, and stakeholder reporting.
ARCHITECTURE VALIDATED
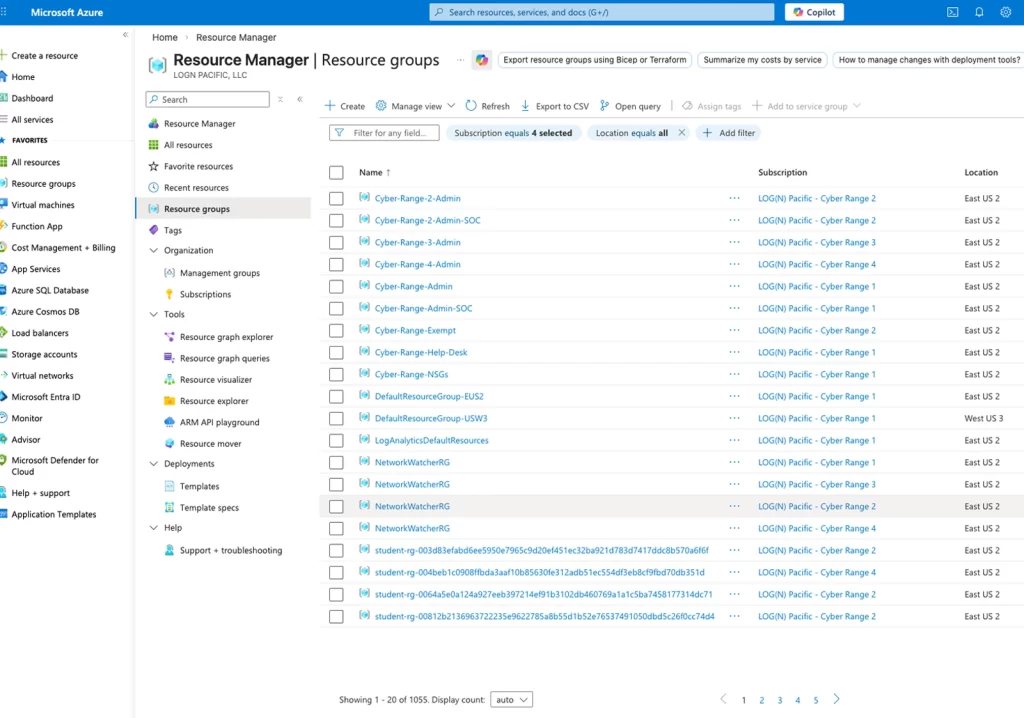
Hands-On Experience in Azure
All students operate within a shared Azure tenant — just like in a real corporate environment. Everyone has read access across all subscriptions, and each student holds admin rights over their own resource group to provision virtual machines for sandboxing and honeypotting. The environment is intentionally not isolated: permissions mirror real-world settings, and students are trained to work responsibly and stay mindful of shared resources. No student-induced major incidents to date.
NIST COMPLIANT
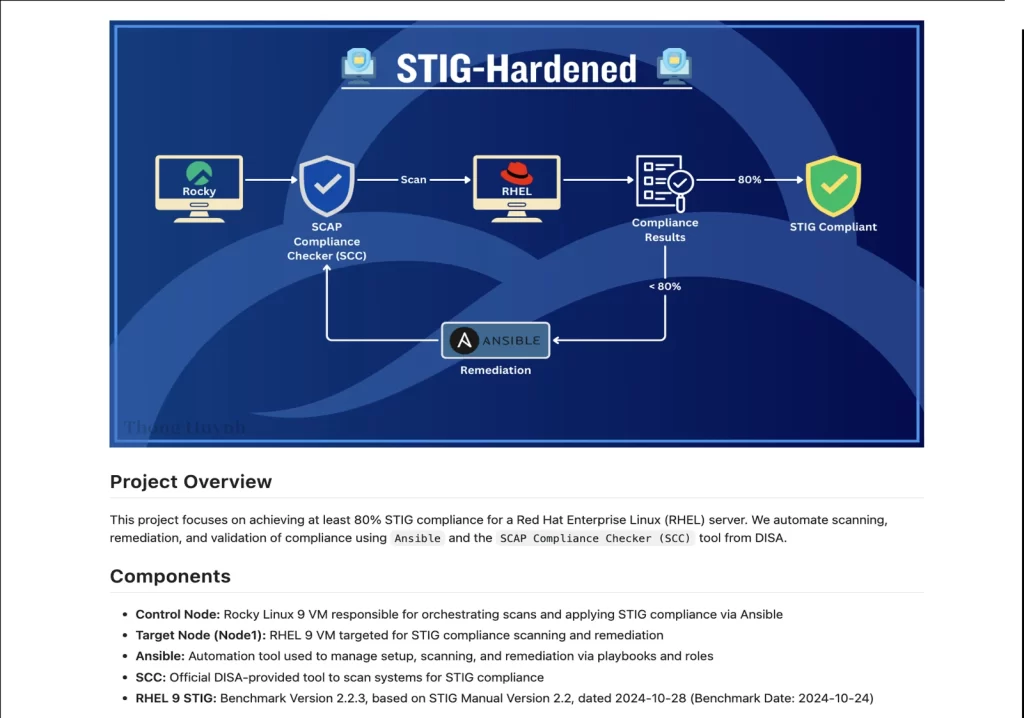
Professional Documentation
Every student produces documentation that meets real enterprise standards. Incident reports follow the NIST 800-61 framework, STIG hardening checklists cover both Windows and Linux systems, and vulnerability remediation plans are structured around risk prioritization. The goal isn’t just technical accuracy — students are trained to create work that is clear, audit-ready, and immediately usable by a security team from day one.
OPERATIONAL EXPERIENCE
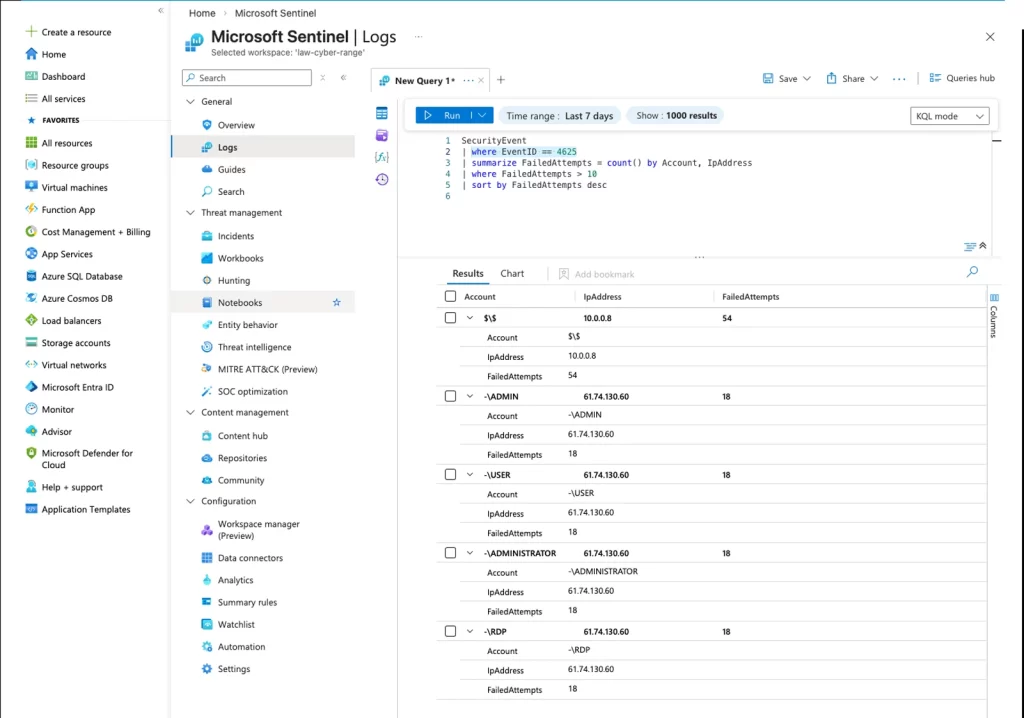
Live Threat Hunts & CTFs
Students conduct real telemetry analysis using KQL in Microsoft Sentinel, our production SIEM. Twice a month, threat hunts put candidates through live attack scenarios with actual prize competitions on the line. Log sources span Defender for Endpoint (EDR), email telemetry, cloud applications, and externally ingested feeds. To claim one of the 10 prize spots per hunt, students must submit a detailed threat report documenting their findings and reasoning — creating a shared learning resource for the entire cohort.
3-12 Months
From beginner to hire-ready
in our production environment
Enterprise Tools
Tenable, Defender, Sentinel, Azure
the stack you already use
Real Operations
Not labs. Not sims. Live vulnerabilities
and active threat hunting.
BEYOND THE TECHNICAL
The question you're really asking
"Will they fit on my team?"
Technical skills are table stakes. Here’s what separates candidates who actually contribute from those who need hand-holding.
20+
Peer Assists
They Explain, Not Just Answer
→ They can explain technical concepts clearly and help teammates grow.
Weekly
Live Hunts
They Stay Calm When It Counts
→ They've practiced incident response under pressure and communicate findings clearly.
Self
Directed
They Figure It Out
→ They take initiative and troubleshoot independently rather than waiting for instructions.
THE JOSH STANDARD
How We Build Combat-Ready Professionals
Founded by Josh Madakor (213K+ YouTube subscribers), Cyber Range rejects the “learn theory, pray for jobs” model. We train in live production environments using the same tools your team uses today.
STEP01
Validation
-
Real Azure/AWS tenant with 1,000+ resource groups
-
Admin rights over personal resource group
-
VM provisioning for sandboxing & honeypotting
-
No simulations — actual enterprise environments
STEP02
Compliance
-
NIST 800-61 incident reports & documentation
-
STIG hardening for Windows & Linux systems
-
Vulnerability remediation plans with risk prioritization
-
Documentation standards matching Fortune 500 SOPs
STEP03
Combat
-
Bi-weekly threat hunts with real prize competitions
-
Live KQL analysis in Microsoft Sentinel
-
Timed incident response under real pressure
-
Peer-reviewed write-ups & post-mortems
STEP04
Leadership
-
GitHub portfolio curation & optimization
-
Technical interview preparation (not just behavioral)
-
Ongoing mentorship & post-placement support
-
Salary negotiation coaching based on market data
We Want to Hear From You
Tell us about your security stack and hiring needs.